Journey
You should never trust them.
Sometime around 2007, with the introduction of OS X 'Tiger', Apple's filesystem dispensed with their resource forks and Finder info, instead integrating them all into the all-new extended attribute scheme. Many filesystems for many operating systems admit of extended attributes, but none quite the way Apple concocted.
The extended attribute is data for most 'anything you like' and most often stored in binary XML format. An extended attribute's name often builds on the 'reverse domain' idea, such as com.rixstep.application.
Apple also introduced the new command-line tool xattr.
XATTR(1) SD General Commands Manual XATTR(1)
NAME
xattr -- display and manipulate extended attributes
SYNOPSIS
xattr [-lrsvx] file ...
xattr -p [-lrsvx] attr_name file ...
xattr -w [-rsx] attr_name attr_value file ...
xattr -d [-rsv] attr_name file ...
xattr -c [-rsv] file ...
xattr -h | --helpApple also exposed the new underlying system API - to list, get, set, and remove extended attributes.
ssize_t
getxattr(const char *path, const char *name, void *value,
size_t size, u_int32_t position, int options);
ssize_t
listxattr(const char *path, char *namebuf, size_t size,
int options);
int
removexattr(const char *path, const char *name, int options);
int
setxattr(const char *path, const char *name, void *value,
size_t size, u_int32_t position, int options);Rixstep introduced their GUI-based Xattr.app a few weeks later, together with a command-line version.
XaBatch.app followed shortly thereafter. XaBatch.app was initially a command-line tool for system administrators using its own proprietary script language.
Security on Apple's new mobile device iPhone was initially perplexing to say the least. All user processes ran on the system root account, meaning any iPhone application could be hacked to take control of the entire device.
This was abruptly changed after a few 'point' updates to the iPhone OS (originally touted as 'OS X') and the introduction of 'code signing'. Starting at that point, all user applications had to be sealed by Apple's own root-level certificate.
Third-party software for iPhone had to be submitted to Apple to obtain this seal. Apple reserved the right to reject any software product they didn't like. The iPhone OS kernel's launch code was modified to require the presence of Apple's root-level certificate.
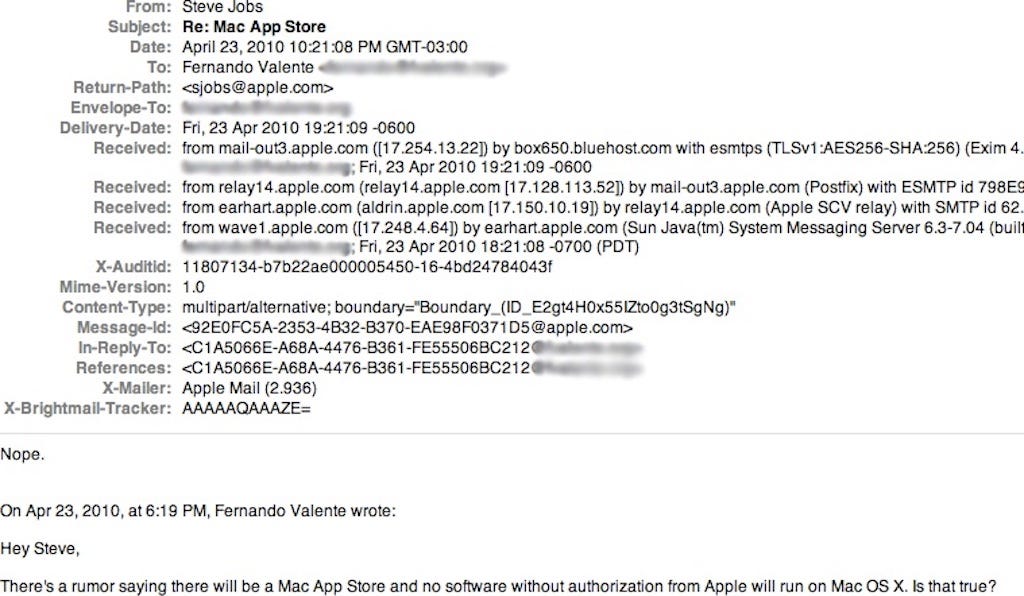
Many saw a portent of things to come. Rixstep 'trolled' Steve Jobs himself to see what he was up to and to get him to commit to not imposing restrictions the OS X platform.
Tim Cook replaced Steve Jobs and the juggernaut kept moving forward. A cursory analysis showed that a lot of money (billions) was involved. Both Forbes, Fortune, and the New York Times predicted hard times ahead for Apple as the smartphone market became saturated.
Apple tried raising iPhone prices, then lowering them, but the market didn't react. Apple finally understood they'd have to return to their computer OS again.
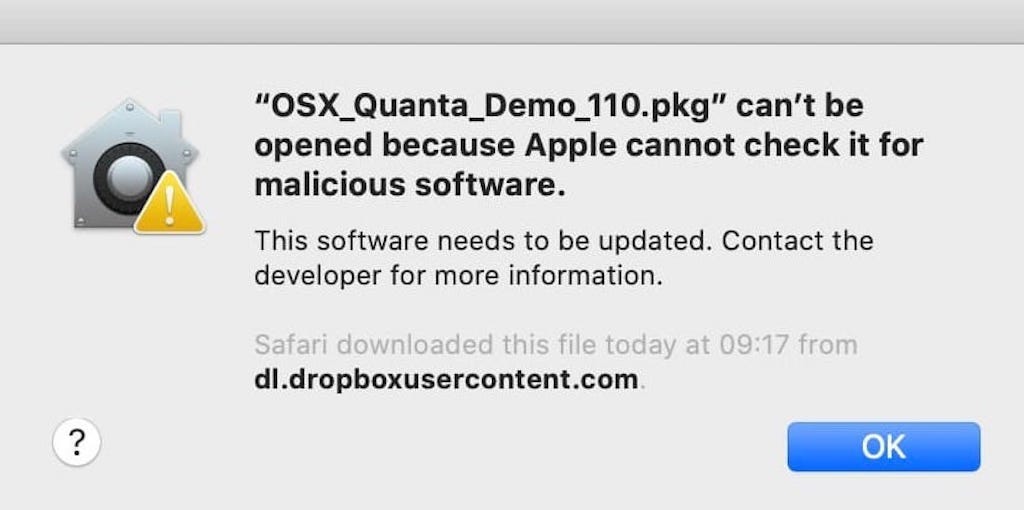
Apple's next tack was to introduce their 'kiddie pool' system known as 'notarisation', the purpose of which was to get independent software houses used to the idea of letting Apple approve or reject their products and control their revenue streams.
But behind it all loomed a reality they couldn't budge. Computer software was a different ballgame. Millions of applications, components, drivers would never accept the regimen that Apple imposed on their mobile platform.
Yet inducing third-party software vendors to use the App Store for distribution was potentially a very lucrative game, estimated at the time to be worth at least $6 billion per annum.
Apple recently announced that they're reducing their 30% 'tax' to 15% for lesser vendors, which means not only that they're taking a hit of at least $3 billion but also that they haven't succeeded in getting third-party software houses to sign up, and that's an encouraging sign.
Apple's OS X was no longer a free market (if it had ever been). This meant that corporations that had invested time and money in Apple systems were going to be hard hit.
To this end, Rixstep began research and development of software to combat Apple.
The first discovery, after digging into Apple's 'Gatekeeper' scheme, was that their own Safari browser announced downloads through the OS notification system.
This resulted in enhancements to Rixstep's Lightman.app, amongst others. Downloads were immediately purged of their extended attributes which Apple's launch code could thereafter use to place them in Gatekeeper's 'quarantine'.
Once in 'quarantine', Apple's Gatekeeper would otherwise use scare tactics to discourage use, and make it nearly (but not completely) impossible to open them.
A full analysis of the Apple mechanisms at work was conducted with the new Rixstep utility Changes.app. Apple had developed a 'change notification' system akin to Microsoft's but on steroids. This system reports on filesystem activities in excruciating detail.
Changes.app led to the development of the actual 'Apple-killer' (or Gatekeeper-killer) application Keymaster.app. 'All your attribute are belong to us.' Keymaster.app: it lets corporations conduct 'business as usual' without being encumbered at every turn by Apple's false intimidations.
Am I Secure?
The most important important question for users of Apple's computer OS is: am I secure? Apple have done everything they can to convince that you are not secure, despite their long advert campaigns to the contrary.
The only reason to choose an Apple computer over a Windows computer is security.
Apple is not the 'most secure' Unix. Not by a long shot. If security is your bag, then IBM's Red Hat should be something you consider, or the ultimate OpenBSD.
But the stretch between any two Unix systems is nothing compared to the non-breachable gap between Microsoft Windows and - literally - anything else.
Microsoft Windows doesn't have a security model. It's built on top of MS-DOS which is a single-user system where physical access to the computer is the only impediment to total control.
Apple's computer OS is a derivative of BSD Unix, a project at UC Berkeley led by Bill Joy of Sun Microsystems.
Were you secure on your Apple computer all those years when Apple ran their 'Mac vs PC' adverts about 'Cancel or Allow'? You're just as secure today.
You didn't have Gatekeeper back then and you don't need it now.
Over time you'll probably have to abandon Apple as a corporate platform. Their products are overpriced, they have no exit strategy, they're screwing people with their monopolies and are infamous for 'bait and switch' double-crosses.
But, for now, you can survive almost like before with Rixstep's Keymaster.app.
(And there's a free version available.)
Attribute-Awareness
Rixstep's entire software arsenal is aware of extended attributes. Xfile, Xfind, Xscan, Tracker, and more bring extended attributes to your attention so you can see what's really going on in your local machine and in your network. Rixstep editors such as PlistEdit and Rixedit do what they can to minimise the proliferation of extended attributes.
No more .DS_Store. A neutered Gatekeeper. Give it a try.